OK, this is complicated and you will need to bear with me. The problem is that somewhere in your server's compile chain you're either missing the OpenSSL Certification Authorities cache or it's out of date.
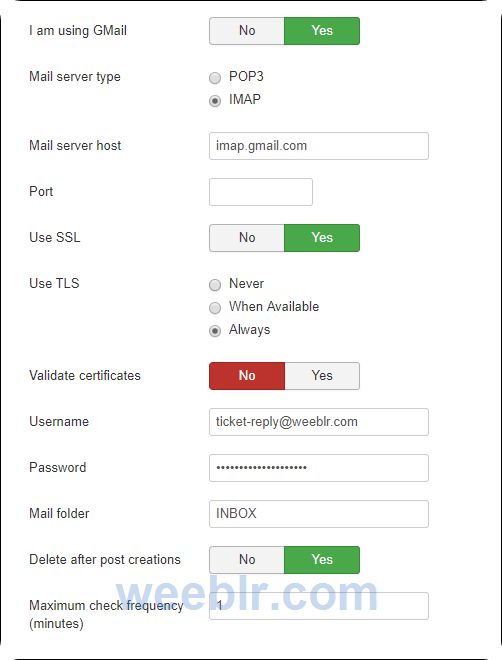
ATS uses PHP's IMAP extension to talk to email servers. The PHP IMAP extension is either statically linked against libc-client.a or dynamically linked against libc-client.so. libc-client is compiled against OpenSSL. Therefore all SSL features end up being handled by OpenSSL.
When OpenSSL starts an encrypted connection it eventually retrieves the remote party's certificate and certificate chain and needs to validate it. It does so against its Certification Authorities cache. This can be either a single file (think cacert.pem) or a directory, the latter being the default on CentOS / RHEL.
If you are not sure where that is you can run
var_dump(openssl_get_cert_locations()) in a PHP script on your server to find out. If these locations are empty, do not actually exist on your server or they contain outdated certificates the certificate validation will fail.
I am not entirely sure if the
OpenSSL runtime configuration in php.ini affects where IMAP will look for its CA cache but you can try. On all my dev servers I have set openssl.cafile to a local path (/opt/cacert/cacert.pem) which contains
the cacert.pem file from cURL. I'm also using up-to-date macOS, Windows and Ubuntu Server installations which do have updated root CA caches so I'm not sure which of the two factors is what makes things work for me.
Nicholas K. Dionysopoulos
Lead Developer and Director
🇬🇷Greek: native 🇬🇧English: excellent 🇫🇷French: basic • 🕐 My time zone is Europe / Athens
Please keep in mind my timezone and cultural differences when reading my replies. Thank you!