Note
This feature is only available in the Professional release
Warning
This feature is only available on servers running the Apache web server. If your server is using IIS or NginX the button to launch this feature will not be shown. If you are using Lighttpd, Litespeed or any other server software you will see a button to launch this feature but this feature may not have any effect. If unsure please consult with your host about their server's support of .htaccess files.
One of the most important aspects of managing a web site hosted on an Apache server is being able to fine-tune your .htaccess file. This file is responsible for many web server level tweaks, such as enabling the use of search engine friendly (SEF) URLs, blocking access to system files which should not be accessible from the web, redirecting between pages based on custom criteria and even optimising the performance of your site. On the downside, learning how to tweak all those settings is akin to learning a foreign language. The feature in Admin Tools helps you create such a file with a user-friendly interface.
Important
Some prepackaged server bundles and some live hosts do not allow using .htaccess files to override server settings. If it is a local server, edit your httpd.conf file and modify every AllowOverride line to read:
AllowOverride All
If you are on a live host, please consult your host about the possibility of them allowing you to use this feature on your site.
Tip
If you ever want to revert to a "safe default", just set all of the options on this page to "Off" and click on "Save and create .htaccess". This will create a very basic .htaccess file which is essentially the same as the one shipped with Joomla! (htaccess.txt) without any of the optional sections.
The top part of the .htaccess maker page contains the standard toolbar buttons you'd expect:
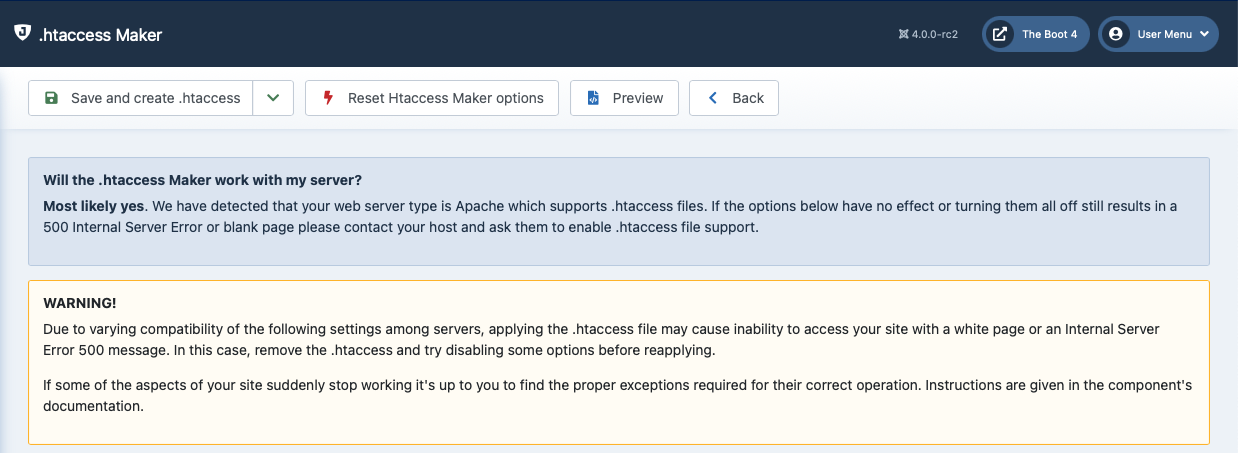 |
saves the changes you have made in this page's options and creates the new
.htaccessfile. If you already had a.htaccessfile on your site, it will be renamed to.htaccess.admintoolsbefore the new file is written to disk.(visible after clicking the dropdown arrow next to the previous button) saves the changes you have made in this page's options without creating a new
.htaccessfile. This should be used when you have not decided on some options yet, or if you want to preview the generated.htaccessfile before writing it to disk.Reset Htaccess Maker options will reset all options on the page to the default settings you'd see when first installing Admin Tools. Please note that this is NOT the same as turning off every option! The default settings have several features turned on. Use this button only when you feel you've messed up so bad you don't even know where to begin fixing things.
pops up a dialog where you can see how the generated
.htaccessfile will look like without writing it to disk. This dialog shows the saved configuration. If you have modified any settings they will not be reflected in there until you click either of the save buttons.The button takes you back to the Control Panel page.
Below the toolbar there are five panes with different options, described below. Before you do that, please read and understand the following warning. Support requests which indicate that you have not read it will be replied with a link back to this page.
Please bear in mind that depending on your web server settings, some of these options may be incompatible with your site. In this case you will get a blank page or an Internal Server Error 500 error page when trying to access any part of your site. If this happens, you have to remove the .htaccess file from your site's root directory using an FTP application or the File Manager feature of your hosting control panel. Your old .htaccess file is saved as .htaccess.admintools. You can rename that file back to .htaccess to revert to the last known good state. If you are unsure how this works, please consult your host before trying to create a new .htaccess file using this tool.
Some prepackaged server environments, like WAMPserver, do not enable Apache's mod_rewrite module by default, which will always result in an Internal Server Error upon applying the .htaccess file. In this case you are strongly suggested to enable it. On WAMPserver you can click on its tray icon, go to Apache, Modules and make sure rewrite_module is checked. On other server environments you have to edit your httpd.conf file and make sure that the LoadModule mod_rewrite line is not commented out (there is no hash sign in front of it). Once you do either of these changes, you must restart your server for the change to become effective.
If this is the first time you are using the .htaccess Maker we recommend that you begin by setting all options to No and then enable them one by one, creating a new .htaccess file after you have enabled each one of them. If you bump into a blank or error page you will know that the last option you tried is incompatible with your host. In that case, remove the .htaccess file, set the option to No and continue with the next one. Unfortunately, there is no other way than trial and error to deduce which options may be incompatible with your server.
Other important things you can add to your .htaccess
Some things cannot be added as features to the .htaccess Maker because the interface would become truly unwieldy. However, there are tools which can generate rather compact .htaccess rules which you can add to .htaccess Maker, in the Custom .htaccess rules at the top of the file section. Here we'd like to point you to some of them.
Content security policy (CSP)
It mitigates the risk of cross-site scripting and other content-injection attacks. Joomla 4 and later includes a component which can do that for you. The downside is that the component's options only apply to the pages generated by Joomla 4 and later versions.
Alternatively, you can read more about it on the dedicated site for this feature. There is a simple tool which allows you to generate the required .htaccess code for the CSP feature according to your preferences. Keep in mind that when you restrict the scripts' origin you should keep in mind that several extensions (including many templates) will load their scripts off a third party CDN which must be explicitly allowed or your site will no longer work!
Caution
It is very easy to break access to your site using a malformed or not very well thought out CSP. Make sure you know how to find and remove the .htaccess file to regain access to your site should that occur.
We cannot help you create or troubleshoot a CSP for your site.
Custom error documents
Most hosting control panels allow you to specify custom HTML pages for common server error pages. The most important ones are for errors 403 (Access Forbidden), 404 (Not Found) and 500 (Internal Server Error). It's always a good idea showing a nicely designed page instead of the default, text-only, ugly page of Apache for these error messages!
Beware of your hosting folder structure
If you have created subdomains please make sure that their web root is outside of the web root of your main site.
For example, this directory layout is CORRECT:
<youraccountfolder>
+--public_html(Mainsite'swebroot)
+--foobar_html(Subdomain'swebroot-CORRECT)
Whereas this directory layout is WRONG:
<youraccountfolder>
+--public_html(Mainsite'swebroot)
+--foobar_html(Subdomain'swebroot-WRONG)
The reason is explained in Apache's official documentation and has to do with the way the .htaccess directives cascade across filesystem directories, not configured domains / subdomains:
The configuration directives found in a | ||
| --Apache Official Documentation | ||
If you end up with a subdomain's web root under the main site's web root the .htaccess file of the main site will also be used in the subdomain. Even if you create a different .htaccess file in the subdomain, the way Apache applies the parent directory's .htaccess directives will get in the way. You will have several problems which will make your site appear broken, files inaccessible etc.
 |
- Disable directory listings (recommended)
When disabled, your web server might list the files and subdirectories of any directory on your site if there is no index.html file inside it. This can pose a security risk, so you should always enable this option to avoid this from happening.
- Protect against common file injection attacks
Many attackers try to exploit vulnerable extensions on your site by tricking them into including malicious code hosted on the attacker's server. Enabling this option will protect your server against this kind of attacks. This works by preventing any URL which references an http:// or https:// URL in the query string. Sometimes these are legitimate requests. For example, some gallery components use them. In this case you are recommended to use the RFIShield (Remote File Inclusion protection) in the Web Application Firewall and turn this .htaccess Maker option OFF.
- Block access to configuration.php-dist and htaccess.txt
These two files are left behind after any Joomla! installation or upgrade and can be directly accessed from the web. They are used by attackers to tell the Joomla! version you are using, so that they can tailor an attack targeting your specific Joomla! version. Enabling this option will "hide" those files when accessed from the web (a 404 Not Found page is returned), tricking attackers into believing that these files do not exist and making it slightly more difficult for them to deduce information about your site. This option also hides the web.config.txt file included in Joomla! 3 and later for use with the IIS server.
- Protect against clickjacking
Turning on this option will protect you against clickjacking. It does so by preventing your site's pages to be loaded in a, Frame, IFrame or Object tag unless this comes from a page inside your own site. Please note that if your site relies on its pages being accessible through frames / iframes displayed on other sites (NOT on your site displaying content from other sites, that's irrelevant!) then you should not enable this option. If unsure, enable it.
- Reduce MIME type security risks
Internet Explorer 9 and later, as well as Google Chrome, will try by default to guess the content type of downloaded documents regardless of what the MIME header sent by the server. Let's say a malicious user to upload an executable file, e.g. a .EXE file or a Chrome Extension, under an innocent file extension as .jpg (image file). When a victim tries downloading this file, IE and Chrome will try to guess the file type, identify it as an executable file and under certain circumstances executing it. This means that your site could be unwittingly used to serve malware. Such an event could result in your site being added to a list of known bad sites by browser makers and cause their browsers to display a warning to users when visiting your site. By enabling this feature you instruct IE and Chrome to respect the file type sent by your server, eliminating this issue. See the relevant MSDN article for more information.
- Reflected XSS prevention
When enabled the browser will be instructed to prevent reflected XSS attacks. Reflected XSS attacks occur when the victim is manipulated into visiting a specially crafted URL which contains Javascript code in it. This URL leads to a vulnerable page which outputs this Javascript code verbatim in the page output ("reflects" the malicious code sent in the URL).
This is a commonly used method used by attackers to compromise web sites, especially when a zero-day XSS vulnerability is discovered in popular Joomla! extensions or Joomla! itself. The attacker will try to trick the administrators of websites into visiting a maliciously crafted link. If the victims are logged in to their site at that time the malicious Javascript will execute, typically giving the attacker privileged information or opening a back door to compromising the site.
Enabling this option in .htaccess Maker will instruct the browser to try preventing this issue. Please note that this only works on compatible browsers (IE8; Chrome; Safari and other WebKit browsers) and only applies to reflected XSS attacks. Stored XSS attacks, where the malicious Javscript is stored in the database, is NOT prevented. You should consider this protection a safety belt. Not wearing a safety belt in the event of an accident pretty much guarantees serious injury or death. Wearing a safety belt minimises the possibility of injury or death but does not always prevent it. This option is your safety belt against the most common type of XSS attacks. You should use it but don't expect it to stop everything thrown your way. Always keep your software up-to-date, especially when a security release is published!
For more information please consult the relevant MSDN article.
- Neutralise SVG script execution
Send a custom Content Security Policy HTTP header for SVG files which prevents scripts inside them from executing. Doing so will also disable most SVG animations and remove all interactive features from all SVG files.
This option only needs to be enabled if your site is configured in such a way that it allows untrusted users to upload unsanitized SVG files to your site. By default, Joomla does NOT permit this. You'd have to configure it to do so yourself, using the Media Manager's options page and / or a third party extension.
Note that unlike the Site Protection features, this will apply to all SVG files regardless of their location.
- Remove web server and PHP version signature
By default Apache and PHP will output HTTP headers advertising their existence and their version numbers. If you are always using the latest and greatest versions this may not be a problem, but the chances are that your host is using an older version of both software. Giving away the version numbers of the server software in every request makes it trivial for an attacker to obtain information about your site which will help them to launch a tailored attack, targeting known security issues in the versions of Apache and PHP you're using. Enabling this option will mitigate this issue. Please note that this is SECURITY THROUGH OBSCURITY which is NEVER, EVER an adequate means of protection. It's just a speed bump in the way of an attacker, not a roadblock.
You are strongly advised to keep your server software up-to-date. If you're not managing your own server, e.g. you're using a shared host, we very strongly recommend choosing a hosting service which follows this rule. As a simple test, if your server is not currently using one of the PHP versions published in the top right corner of http://php.net (or at most one version earlier, i.e. the third number of the version on your server is one less than the one listed on php.net) the chances are that your server is using outdated, vulnerable server software. Remember that outdated versions of PHP and Apache, even with some security patches backported, CAN NOT be secure. There's a good reason new software versions are published regularly.
- Prevent content transformation
Enabling this feature instructs proxy servers and caches to not convert your content. For example, certain proxy servers (typically found in mobile networks, businesses and ISPs in congested areas) will attempt to scale and aggressively compress images, CSS and Javascript to save bandwidth. This can lead to several issues, from displayed images being a bit off to your site breaking down because the compressed CSS/JS introduced errors preventing the browser from parsing it correctly. With this feature enabled the cache and proxy servers will be instructed to not do that by setting an HTTP header. If they respect the HTTP header (they should, it's a web standard) such issues are prevented.
For more information please consult the formal web standard document RFC 2616, section 14.9.5
- Block access from specific user agents
When enabled, it will block any site access attempt if the remote program sends one of the user agent strings in the User agents to block option. This feature is designed to protect your site against common bandwidth-hogging download bots and otherwise legitimate tools which are more usually used for hacking sites than their benign intended functionality.
- User agents to block
The user agent strings to block from accessing your site. You don't have to enter the whole UA string, just a part of it. The default setting includes several usual suspects.
You can type new entries by clicking at the end of the list, type the entry and press ENTER to accept it. Delete items using the X button next to each entry.
Do note that some server with mod_security or mod_evasive installed will throw an "Access forbidden" message if you try to save the configuration settings when this field contains the word "WGet". If you come across this issue it is not a bug with Admin Tools or Joomla!, it is a server-level protection feature kicking in. Just avoid including the word Wget and you should be out of harm's way.
- Restrict access by IP
Your site will only be accessible by clients whose IP address is within the selected range.
The intended use case is sites which are behind a CDN, load balancer, TLS terminator, reverse proxy, or similar network infrastructure (we will collectively call these “reverse proxy”). In this use case you want your site to not be directly accessible from the public Internet, but you still want your site to be accessible from the reverse proxy. Therefore, you want to add your reverse proxy IP addresses into the list of IPs for the Restrict Access By IP.
This feature can be used either with one of several predefined lists of IP addresses (selected as the most common use cases amongst our clients), or with a custom list of IP ranges you define yourself.
None. Disables this feature. Your site will be directly accessible from the public Internet.Custom List. You provide your own list of IP addresses in the IP ranges allowed access setting below.Internal Network. Access to your site is allowed only by IPv4 and IPv6 addresses reserved for “internal network” use by IANA. The intended use case is sites whose web server sits inside an internal network, their content being pulled by an Internet-accessible load balancer or TLS terminator .CloudFlare. Access to your site is allowed only by IPv4 and IPv6 addresses used by CloudFlare CDN. The intended use case is sites being served through CloudFlare CDN. Prohibiting access from IP addresses which are not used by CloudFlare to pull your site's contents ensures that malicious third parties who know the IP address of your server will be unable to circumvent CloudFlare to attack your site.Sucuri. Access to your site is allowed only by IPv4 and IPv6 addresses used by Sucuri. The intended use case is sites being served through Sucuri. Prohibiting access from IP addresses which are not used by Sucuri to pull your site's contents ensures that malicious third parties who know the IP address of your server will be unable to circumvent Sucuri to attack your site.BunnyCDN. Access to your site is allowed only by IPv4 and IPv6 addresses used by Bunny CDN. The intended use case is sites being served through Bunny CDN. Prohibiting access from IP addresses which are not used by Bunny to pull your site's contents ensures that malicious third parties who know the IP address of your server will be unable to circumvent Bunny to attack your site.
Note
This feature in Admin Tools is designed with commercial hosting in mind where the user is not allowed to modify the VirtualHost and / or the firewall configuration. In this use case, the only possibility for IP access restriction is using the
.htaccess, even at a slight performance penalty (fractions of a millisecond for each document accessed on the server in most cases). While not ideal for performance, it adds a security layer which makes it a positive trade-off.If you are self-hosting your site, or otherwise have access to the Apache configuration, you should transfer the directives implementing this feature into your VirtualHost configuration for performance reasons, then disable it in Admin Tools' .htaccess Maker.
If you have access to your Operating System's firewall you should instead set up the firewall to reject incoming HTTP and HTTPS traffic coming from anywhere outside the allowed IP ranges for even better performance. In this case, you should NOT be using this feature in Admin Tools, nor should you be doing IP restriction in your VirtualHost configuration.
- IP ranges allowed access
This setting only appears when Restrict Access By IP is set to
Custom List. It is the list of IPs, IP/Netmask, or CIDR blocks allowed to access your site.Each entry can be in one of the following formats understood by the web server:
Single IPv4 or IPv6 such as
192.0.2.123or2001:db8::c0ff:ee00.IPv4 with netmask such as
192.0.2.0/255.255.255.0.IPv4 or IPv6 CIDR block such as
192.0.2.0/24or2001:db8::/32.
Important
DO NOT use human readable IP ranges, such as
192.0.2.100-192.0.2.200, or comma / space separated IP address lists. These formats will not work, and may result in your site being inaccessible.While partial IPv4 addresses (such as
192.168) are nominally supported by Apache, they are not supported by Admin Tools because of their very error-prone nature. We recommend using CIDR blocks instead.
Default list of user agents to block
The following is the default list of user agents to block. It is very thorough and seems to be reducing the number of attacks enormously. If you are upgrading from an earlier version you might want to try it out.
acapbot acoonbot acunetix ahrefs alexibot archiver asterias attackbot awario backdor base64_decode becomebot bin/bash binlar blackwidow blekkobot blex blowfish bolt 0 bot for jce bot mailto:[email protected] bullseye bunnys butterfly c99shell careerbot casper casper cazoodlebot checkpriv checkprivacy cheesebot cherrypick chinaclaw chinaclaw choppy clshttp clshttp cmsworld cmsworldmap comodo copernic copyrightcheck cosmos crescent custo datacha default browser 0 demon diavol diibot disco discobot disconnect dittospyder dotbot dotnetdotcom download demon dumbot ecatch econtext ecxi eirgrabber emailcollector emailsiphon emailwolf eolasbot eval eventures express webpictures extract extractorpro eyenetie feedfinder fhscan flaming flashget flicky foobot fuck g00g1e getright getweb! gigabot go!zilla go-ahead-got go-ahead-got-it gozilla grab grabnet grafula gt::www harvest heritrix hmview http::lite httrack httracks ia_archiver icarus6j id-search id-search.org idbot image stripper image sucker indy library interget internet ninja internetseer.com irlbot isc systems irc search 2.1 jakarta java jetbot jetcar jikespider joc web spider kmccrew larbin leechftp libweb libwww libwww-perl liebaofast linkscan linksmanager.com_bot linkwalker loader lwp-download lwp-trivial majestic mass downloader masscan maxthon$ mechanize mfc_tear_sample microsoft url control microsoft.url midown tool miner missigua locator mister pix mj12bot morfeus moveoverbot msfrontpage navroad nearsite net vampire netants netmechanic netspider netzip newt nicerspro nikto ninja nominet nutch octopus offline explorer offline navigator pagegrabber panscient.com papa foto pavuk pcbrowser pecl::http peoplepal petalbot phpcrawl phpshell planetwork pleasecrawl postrank proximic psbot purebot pycurl queryn queryseeker radian6 radiation realdownload reget remoteview rippers 0 rogerbot sbider scan scooter seamonkey$ seekerspid semalt siclab sindice sistrix sitebot sitecheck.internetseer.com sitecopier siteexplorer sitesnagger skygrid smartdownload snoopy sosospider spankbot spbot sqlmap stackrambler steeler stripper sucker superbot superhttp surfbot surftbot sux0r suzukacz suzuran takeout teleport teleport pro telesoft toata dragostea mea pentru diavola true_robots turingos turnit turnitinbot unserializ uri::fetch urllib vampire vikspider voideye web image collector web sucker webalta webauto webbandit webcollage webcopier webfetch webgo is webleacher webreaper websauger webshell website extractor website quester webstripper webvac webviewer webwhacker webzip wells search ii wep search wget widow winhttp woxbot www-mechanize wwwoffle xaldon xaldon webspider xxxyy yamanalab yioopbot youda zermelo zeus zmeu zune zyborg
Important
Blocking by User-Agent string IS NOT A SECURITY FEATURE. Any web client – such as a browser, or a bot – can elect to send a misleading User-Agent string, or no User-Agent string. Since the contents of the User-Agent string are controlled by the remote part initiating the request you cannot trust them, which is why blocking by User-Agent cannot possibly be considered a security feature.